What Is Anomaly Detection? Integration with Monitoring!
In today’s world, where IT infrastructures are becoming increasingly complex, ensuring that systems operate stably and without interruption is only possible through proactive measures, rather than merely reacting to incidents. In this context, Anomaly Detection stands out as one of the most critical components of monitoring processes.
Anomaly Detection: Fundamental Concepts and Technical Infrastructure
Anomaly Detection is the process of detecting deviations of data points observed in a system from normal behavior using statistical and/or machine learning techniques. These deviations can indicate systemic issues such as hardware failure, security breaches, configuration errors, or performance bottlenecks.
Anomalies are examined in three main categories:
- Point Anomaly: A single data deviation at a specific point in time. For example, CPU usage suddenly spiking to 95%.
- Contextual Anomaly: A data point is only anomalous within its specific context. For example, a sudden increase in traffic during nighttime hours.
- Collective Anomaly: Data points that appear normal individually but indicate an anomalous pattern when evaluated together. For example, if several services are sequentially responding slowly, this could be an indicator of a cascading issue.
Technically, anomaly detection is performed using the following methods:
- Statistical Methods: Gaussian distribution, z-score, moving average, interquartile range (IQR).
- Machine Learning Methods:
- Unsupervised Learning: k-means, DBSCAN, Isolation Forest, Autoencoder.
- Semi-supervised Learning: Learning based on normal data, outlier detection.
- Supervised Learning: Classification algorithms (e.g., SVM), if anomaly examples are available.
- Time Series Modeling: Deviation analysis over historical patterns using models such as ARIMA, Prophet, and LSTM.
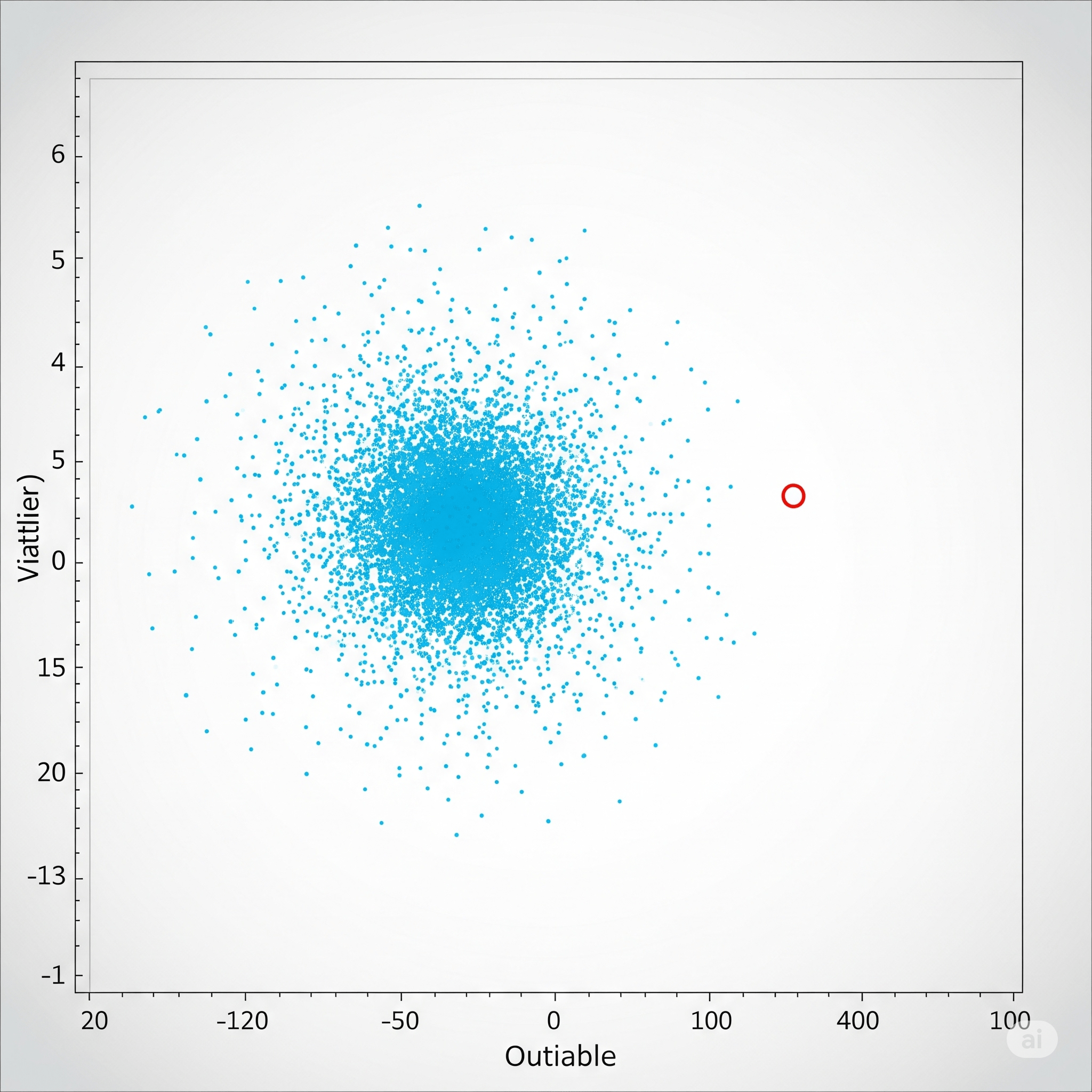
In this image, you can see a scatter plot where most data points are clustered together. However, there is a single data point located quite far from this cluster, standing alone. This single, isolated data point represents a “point anomaly.” Just like in the example we provided—such as a user performing a very large data download at midnight, which is not typical behavior—this isolated point also indicates a situation that deviates significantly from normal behavior. Translated with DeepL.com (free version)
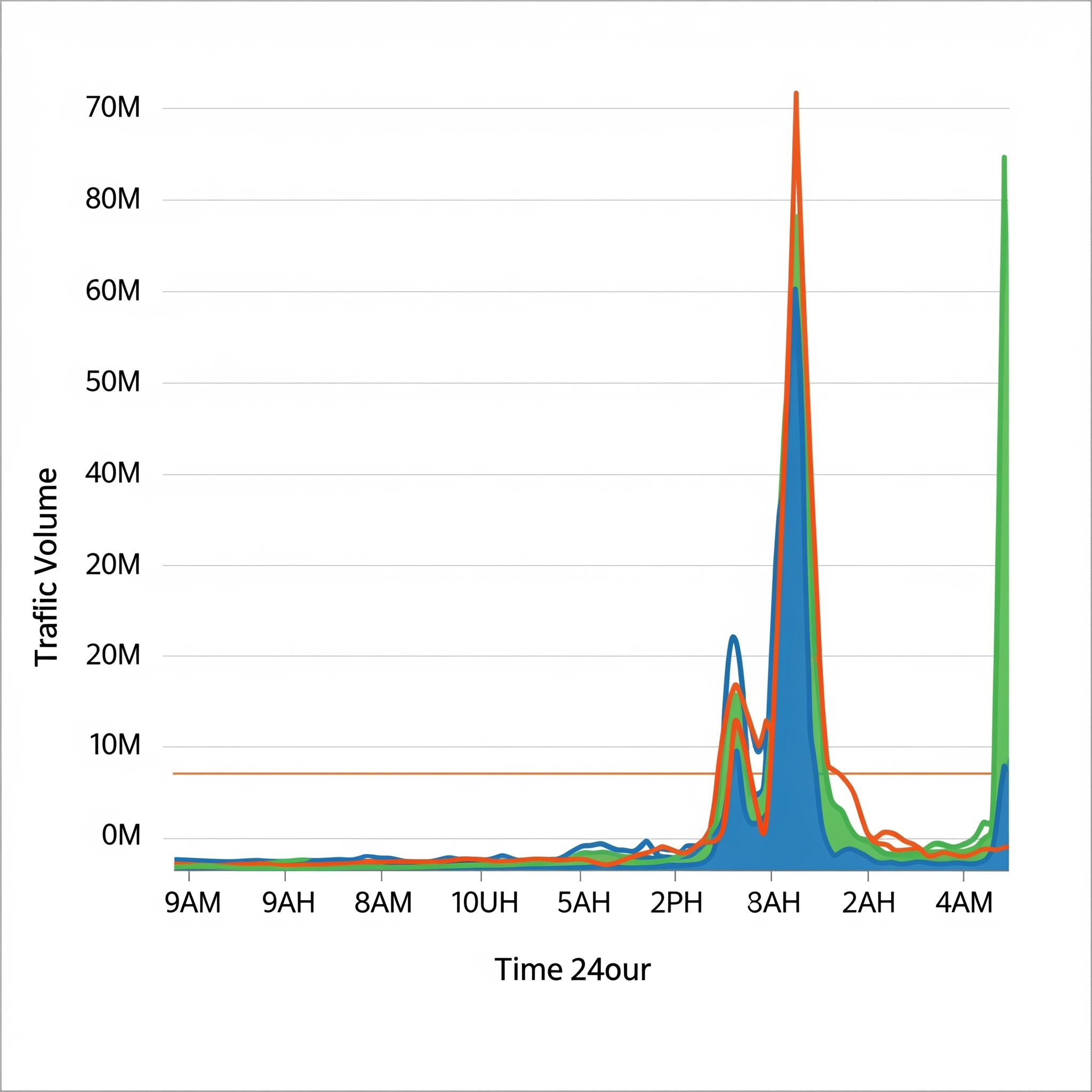
This graph shows a website’s 24-hour traffic volume. During daytime hours (for example, from 9 a.m. to 5 p.m.), traffic volume is high, which is an expected, normal occurrence. However, a similarly high spike in traffic is also observed during late-night hours (for example, from 2 a.m. to 4 a.m.). Normally, traffic should be very low during nighttime hours. Therefore, this high traffic increase occurring at night is considered an anomaly when the context (nighttime) is taken into account. The highlighted section in the image represents this contextual anomaly.
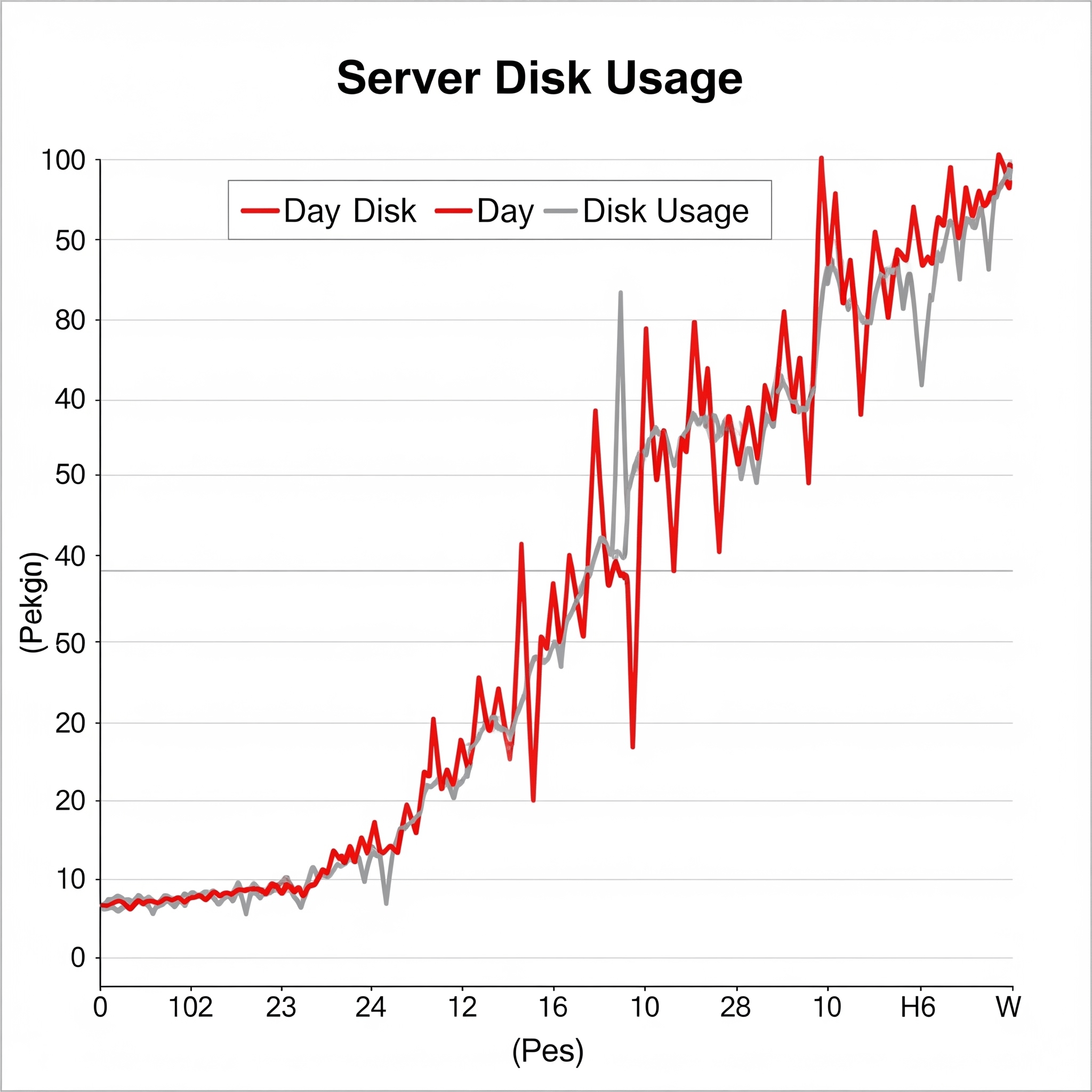
Bu grafikte, sunucu disk kullanımının zaman içindeki değişimi gösteriliyor. Başlangıçta, disk kullanımı normal dalgalanmalar gösteriyor ve belirli bir aralıkta seyrediyor. Ancak daha sonra, disk kullanımının yavaşça ve sürekli olarak arttığı, normal çalışma aralığının üzerine çıktığı bir trend gözlemleniyor.
The Role of Anomaly Detection in Monitoring Systems
Traditional monitoring systems typically operate on a threshold-based approach: “Trigger an alarm when CPU usage exceeds 90%”, “Issue a warning when disk space reaches 95%”, and so on. This approach works well in predictable situations but falls short in the following scenarios:
- Fixed thresholds lose their meaning in dynamic system behaviour.
- The contextual significance of events is overlooked.
- False positive and false negative rates are high.
This is where anomaly detection comes into play. Modern monitoring systems now use predictive analytics and behavioural modelling capabilities to learn the system’s “normal” behaviour and detect deviations from it. This provides the following advantages:
- Proactive Alerts: Behavioural deviations are detected before thresholds are exceeded.
- Lays the Groundwork for Root Cause Analysis (RCA): It shows not just the result, but the pattern in which the problem began to develop.
- Noise Reduction: Irrelevant alerts are filtered out, preventing alert fatigue.
- Correlation: Identifies cascading anomalies based on inter-system relationships (dependency mapping).
Areas of Application and Real-World Scenarios
- Network Monitoring: Sudden packet loss or RTT (Round Trip Time) anomalies.
- Application Monitoring (APM): Contextual increases in user response time.
- Infrastructure Monitoring: Deviations in hardware temperatures and disk I/O values.
- Security Monitoring: Unusual login behaviour, connections from suspicious IP addresses.
Example: CPU Usage and Collective Anomaly
Conclusion: The Evolution of Monitoring is Complemented by Anomaly Detection
Anomaly detection is not merely a feature; it is an integral part of the evolution of monitoring culture. As an increasing number of systems transition to observability-first architectures, anomaly detection engines have become a core component of platforms that analyse metrics, logs and trace data together.
Machine learning systems instead of rules, and proactive intervention capabilities instead of reactive approaches… Anomaly Detection plays a key role in the future of monitoring strategies.
The ODYA Technology team is always here to support you with monitoring solutions and developments. Fill in the form for all your needs, and we’ll get in touch!

