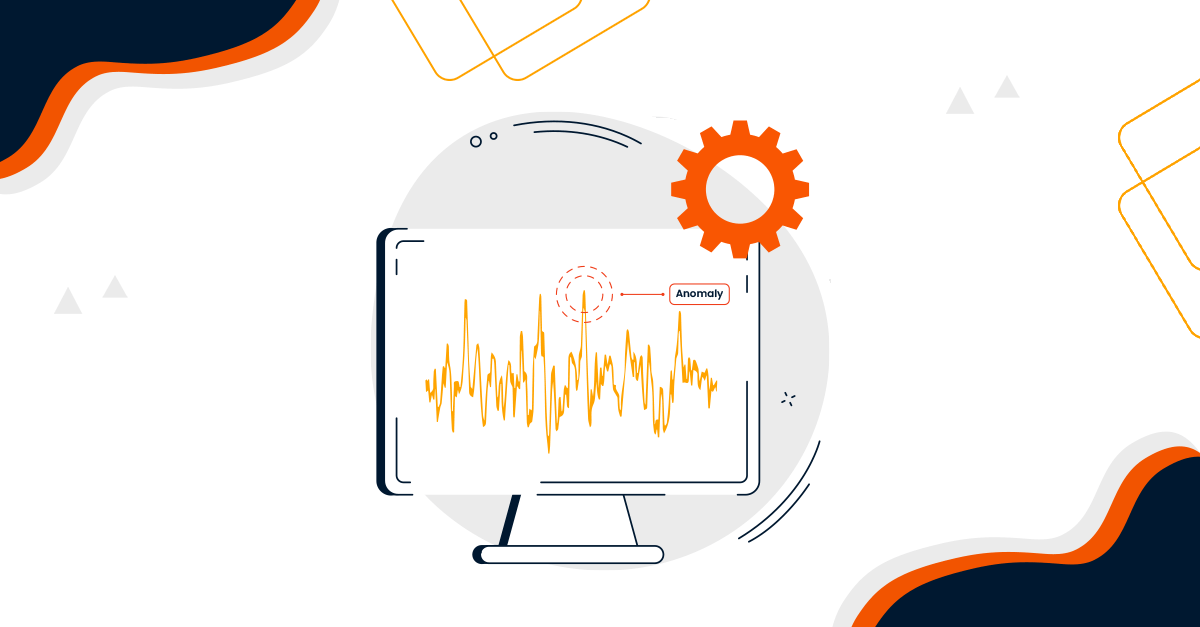
Comparison of Enterprise Monitoring Tools: The Right Tool for the Right Scenario
Comparison of Enterprise Monitoring Tools: The Right Tool for the Right Scenario Enterprise Monitoring Tols · Tool-Agnostic Guide · G2, Capterra & PeerSpot SolarWinds, Zabbi